Product details
CFL Server Password Machine
Product form

Product function
1. Information Center is the cornerstone of information security protection.
2. Support safe landing.
3. Supporting cloud upload
4. Supporting secure databases
5. Supporting Transport Layer Security
6. Support application layer security
7. Support for secure file management
Product advantage
1. On-site certification, timely certification.
2. Application de-centralization and de-storage.
3. Self-certification.
4. Sign in a flash.
5. Dynamic authentication and tiger symbol authentication.
6. Support internal personnel management
7. Support BLP model
Product application
Important Nodes or Information Centers of All Information Industries。
CFL Licensing Authority
Product form

Product function
1. Issuing certificates for network macro-entities.
2. Issue certificates for network micro-entities.
3. In cyberspace, CFL certificate is the logical origin of information security, which constitutes the basis of information security.
Product advantage
1. Compared with the CA of PKI, the construction cost of CFL issuing authority is very low.
2. Support process authentication and field-level security.
3. Supporting one person and one secret can prove safety.
4. Support timely, safe and self-certification.
5. Unique matching block chain
6. Satisfying Zero Knowledge Interaction
7. Fully support today's Information Industry
Product application
Fully support CFL+ Internet + everything. That is to say, the product supports the informatization of all industries.
CFL UKey
Product form

Product function
1. Information security cornerstone of client.
2. Support safe landing.
3. Support for SSL.
4. Supporting secure databases.
5. Support Security Cloud upload.
6. Support secure file management.
7. Support transport layer security.
8. Support application layer security.
Product advantage
1. On-site certification, timely certification.
2. Application de-centralization and de-storage.
3. Self-certification.
4. Sign in a flash.
5. Dynamic authentication and tiger symbol authentication.
6. Support BLP model.
Product application
Client of all information industry。
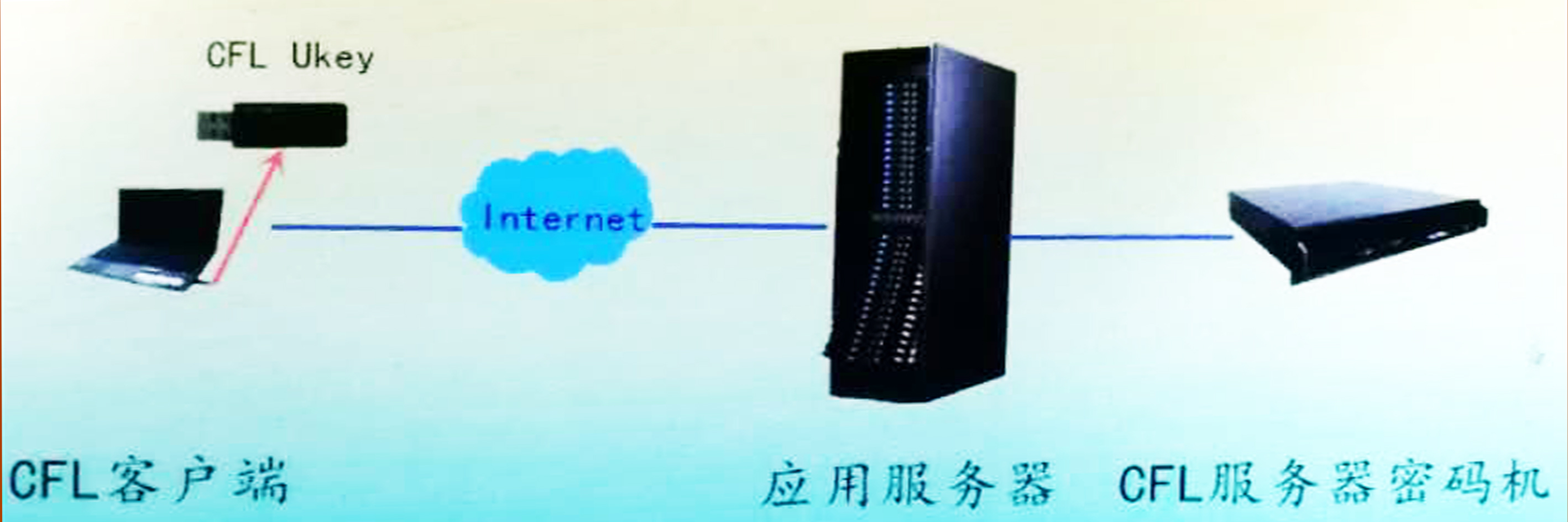
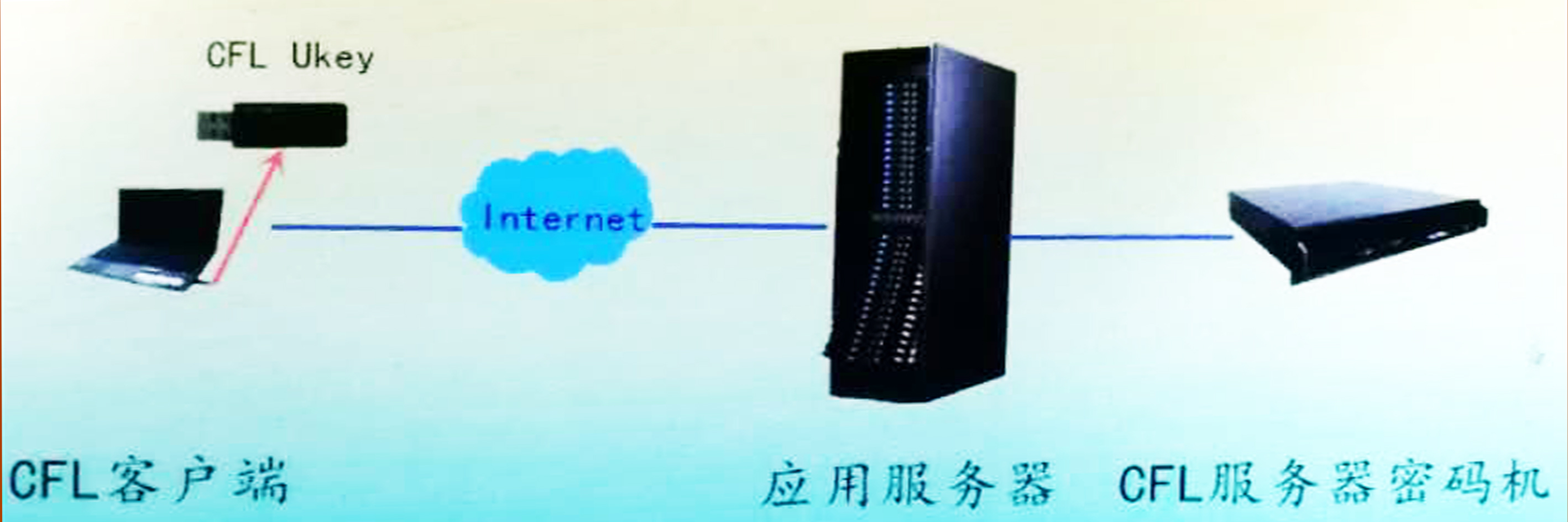
CFL Safe Landing Products
Product Topology
Product function
1. Login based on CFL certificate.
2. Dynamic authentication.
3. Tiger Character Certification.
4. Functional control.
5. Distinguish between self and non-self.
6. Sign in a flash.
Product advantage
1. Provable safety.
2. Zero knowledge interaction.
3. No third-party support is required.
4. De-storage.
5. Decentralization.
6. Authentication in time and on-site.
Product application
1.P2P
2.C/S framework
3.B/S framework
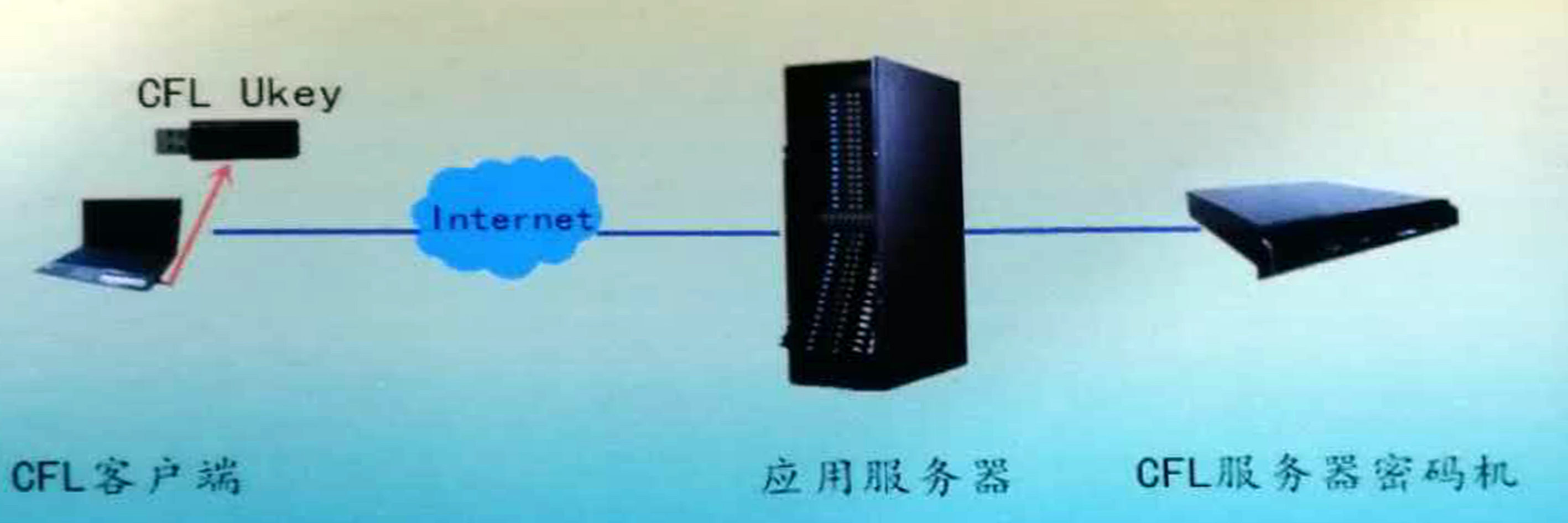
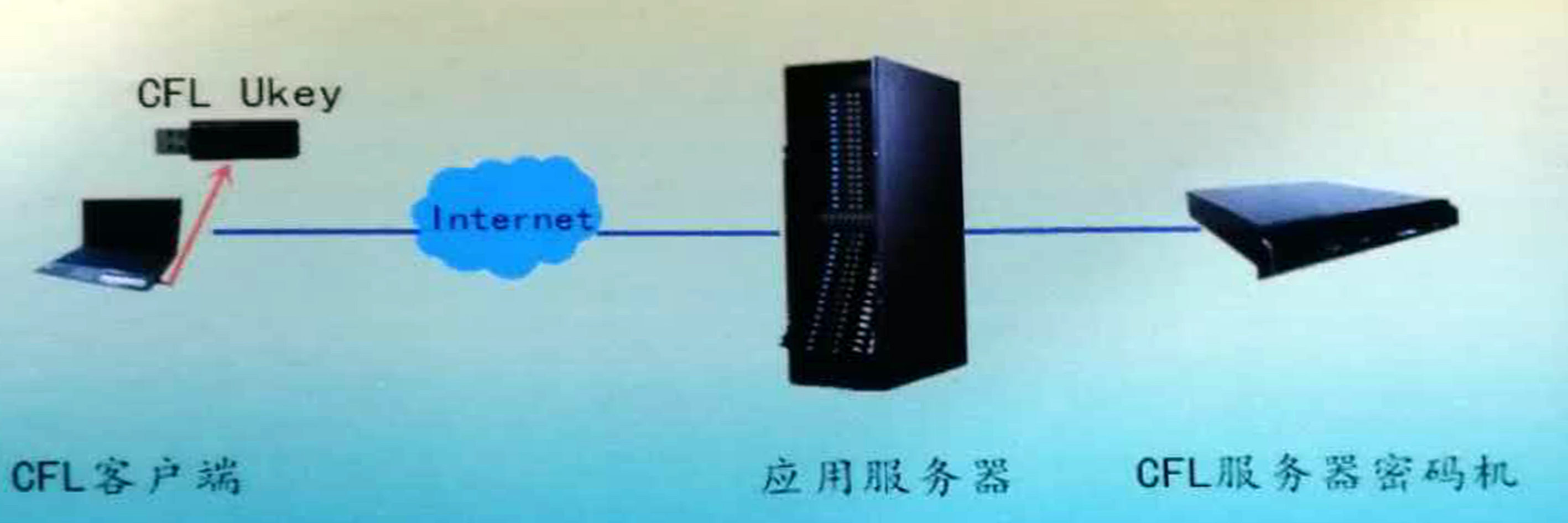
CFL SSL products
Product Topology
Product function
1. Login based on CFL certificate.
2. Dynamic authentication.
3. Tiger Character Certification.
4. Functional control.
5. Distinguish between self and non-self.
6. Sign in a flash.
7. Key Exchange
8. Encryption, decryption and integrity protection communications
Product advantage
1. Provable safety.
2. Zero knowledge interaction.
3. No third-party support is required.
4. De-storage.
5. Decentralization.
6. Authentication in time and on-site.
Product application
1.P2P
2.C/S framework
3.B/S framework
CFL Security Cloud Upload Products
Product Topology

Product function
1. Local file encryption, signature one-way cloud upload.
2. Using cheap public cloud to backup data in different places.
3. Encryption storage and integrity protection of data using cheap public clouds.
Product advantage
1. At present, there is no similar product.
2. Autonomous certification.
3. Active defense.
4. From information security to knowledge security.
Product application
1. Personal or family image data.
2. Hospital image data.
3. Electronic data of enterprises and institutions.
4. Archives backup management.
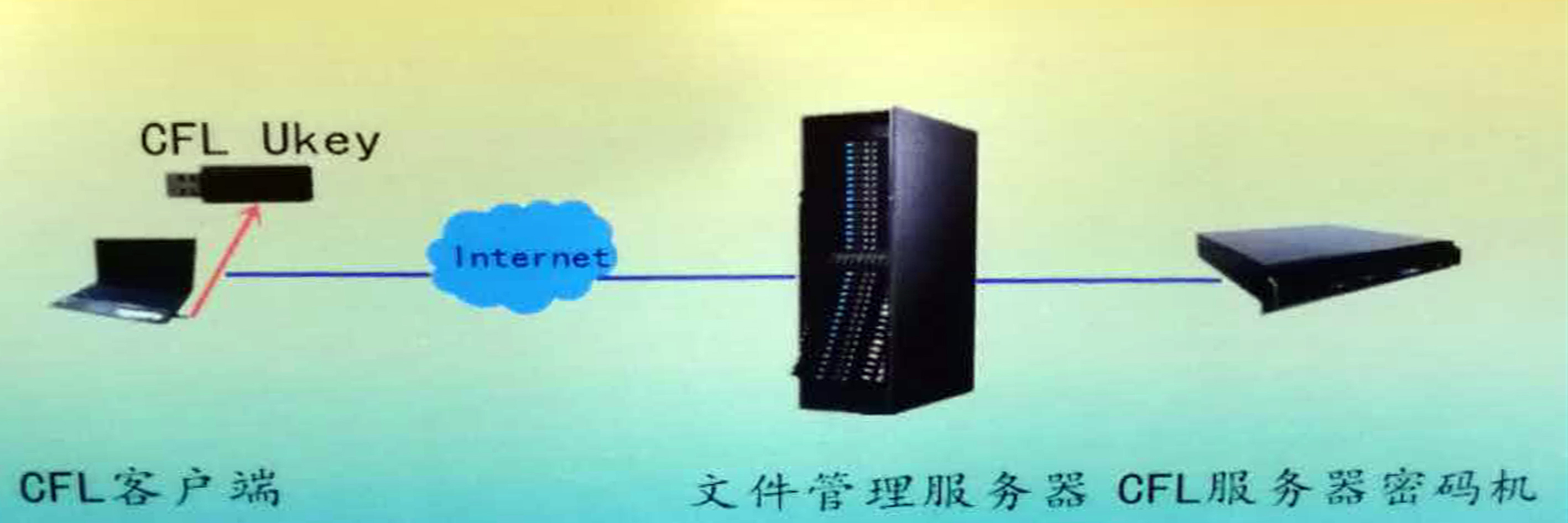
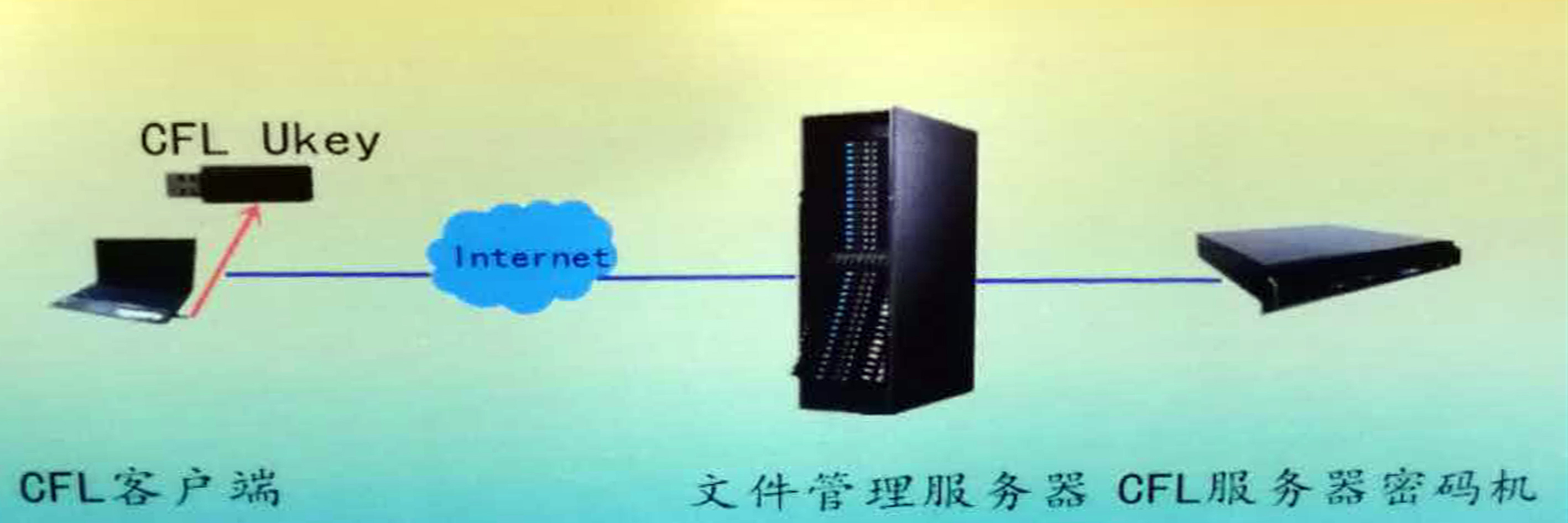
CFL Security Document Management Products
Product Topology
Product function
1. Login based on CFL certificate.
2. Support hierarchical and classified mandatory access control.
3. Support file encryption storage.
4. Support file signature storage.
5. Support document signature authentication.
Product advantage
1. On-site certification, timely certification.
2. Tiger Character Authentication and Dynamic Authentication.
3. Active defense, immune safety.
4. Sign in a flash.
5. Decentralization.
6. Support static and dynamic code security.
Product application
1. Operating system security.
2. File storage security.
3. Support autonomy and control.
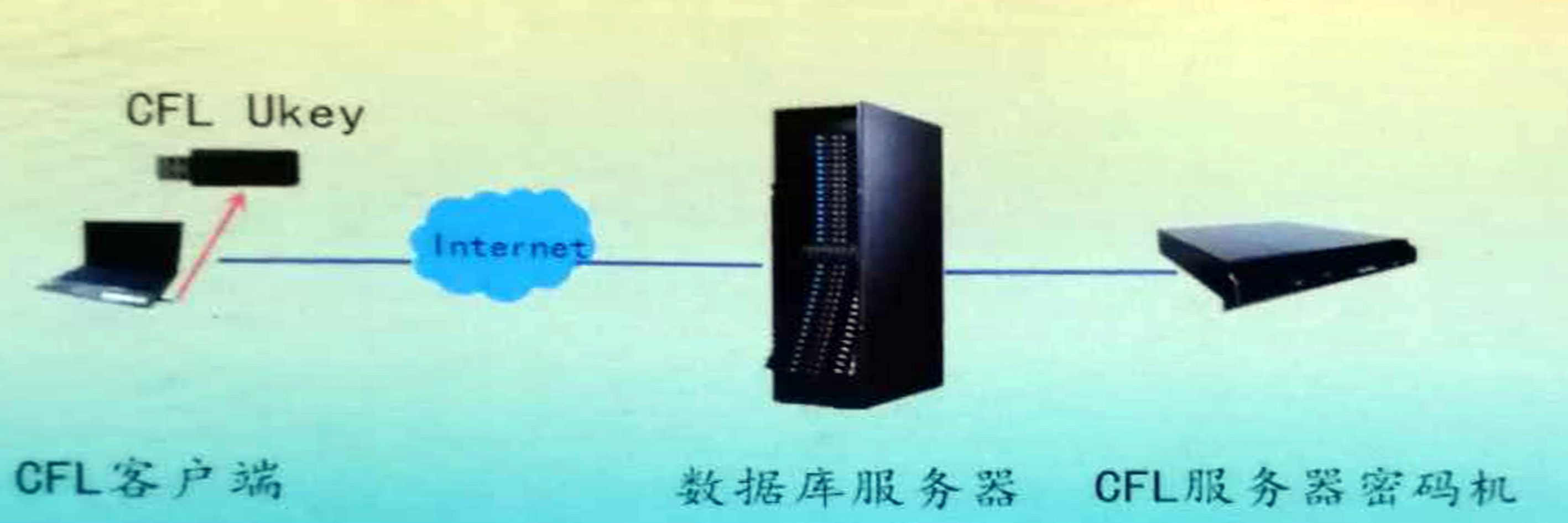
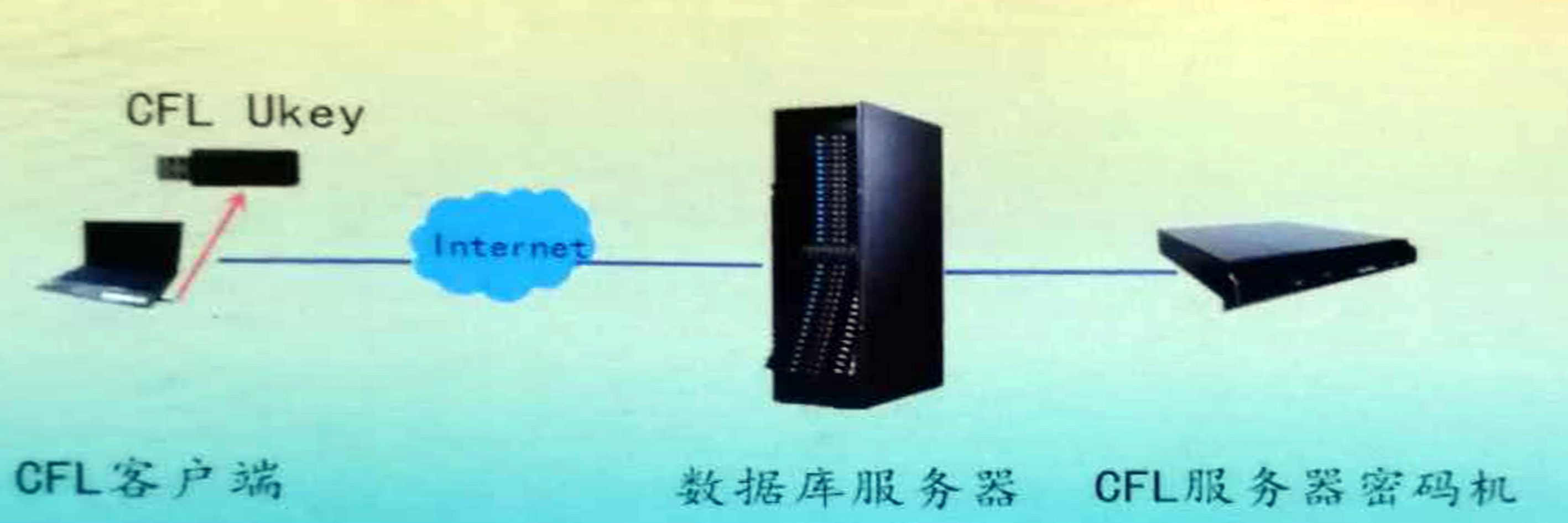
CFL Security Database
Product Topology
Product function
1. Support database login security.
2. Support field-level security.
3. Support hierarchical and classified mandatory access control.
4. Support transmission security.
5. Support application security.
6. Support storage security.
7. Support local file security management.
Product advantage
1. Mark the information security of higher level.
2. On-site certification and timely certification.
3. Tiger Character Authentication and Dynamic Authentication.
4. Active defense, immune safety.
5. Sign on a whim.
6. Safe, fine-grained。
7.Supporting block chains
Product application
All important nodes of information products, information centers and individuals.